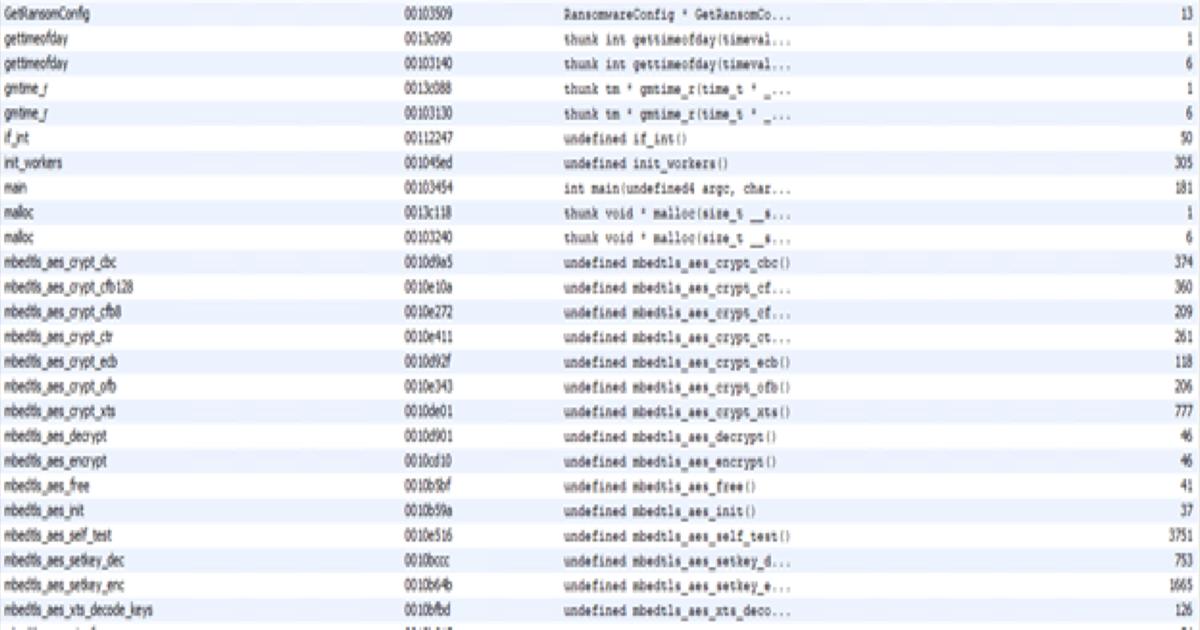
The AI produced malware kill switch
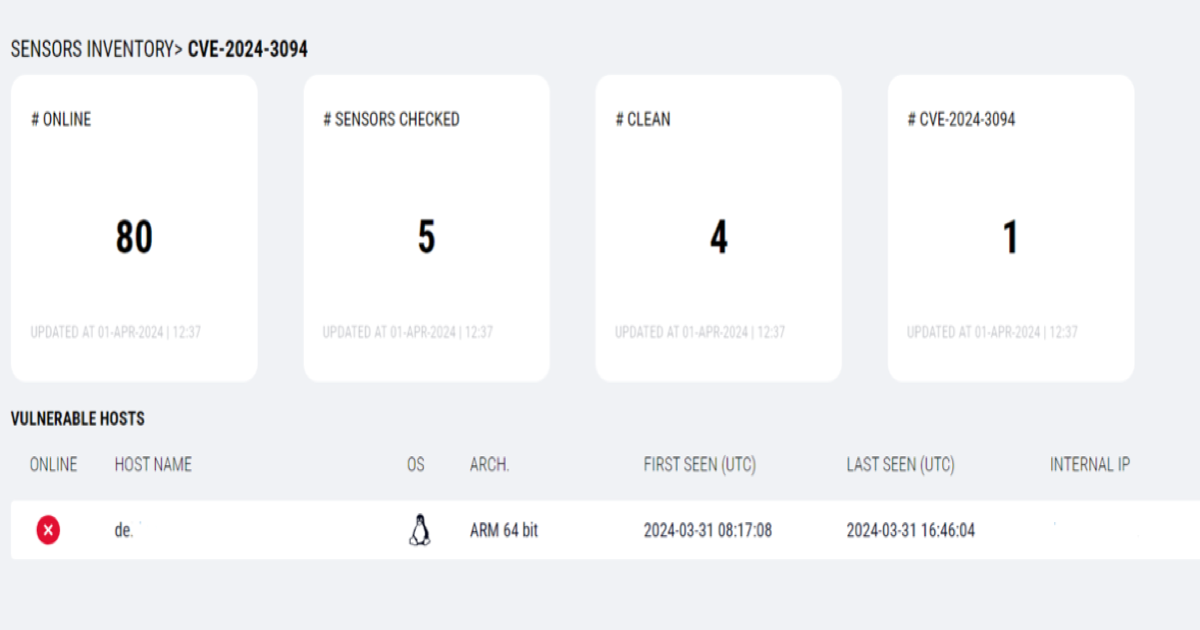
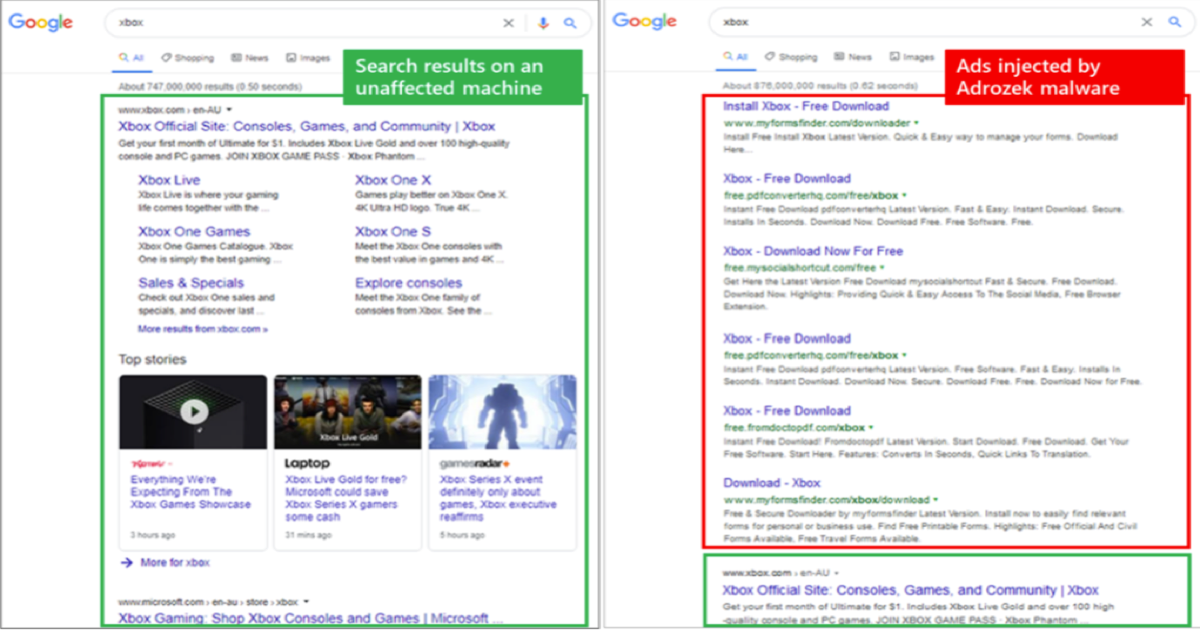
After finding a Discord bot token hardcoded into every WindowsAudit agent binary, we built a monitor, pulled the attacker's own loot dump, and identified 25+ victim organizations — before noticing the architectural flaw that handed us the entire botnet.